DasctfSU6月赛
【困难】pdf_converter
非预期,
1 | public static function invokeFunction($function, $vars = []) |
直接日进去了
预期解:
CVE-2022-41343
当时都搜到了qwq
http://buaq.net/go-129526.html
exp
1 | #!/usr/bin/env python3 |
非预期,
1 | public static function invokeFunction($function, $vars = []) |
直接日进去了
预期解:
CVE-2022-41343
当时都搜到了qwq
http://buaq.net/go-129526.html
exp
1 | #!/usr/bin/env python3 |
midnightCTF,有这么一道题,很是神奇(
1 |
|
起初是认为正则表达式/e能命令执行,赛后复现的时候才发现是Redos
原理很简单,就是利用回溯、贪婪等方式,让正则表达式进行一个大量的工作,这样就产生了一个时间延迟,于是乎就可以直接开始注入了
1 | from lxml import etree |
太菜了,被大佬带进决赛了,最后就签个到
下面部分是我在比赛的时候思考过的
页面一进来,十分的清爽,毛都没有,就一个上传文件的东西
随便传点东西,发现是来者不拒,啥都能传,但啥都干不了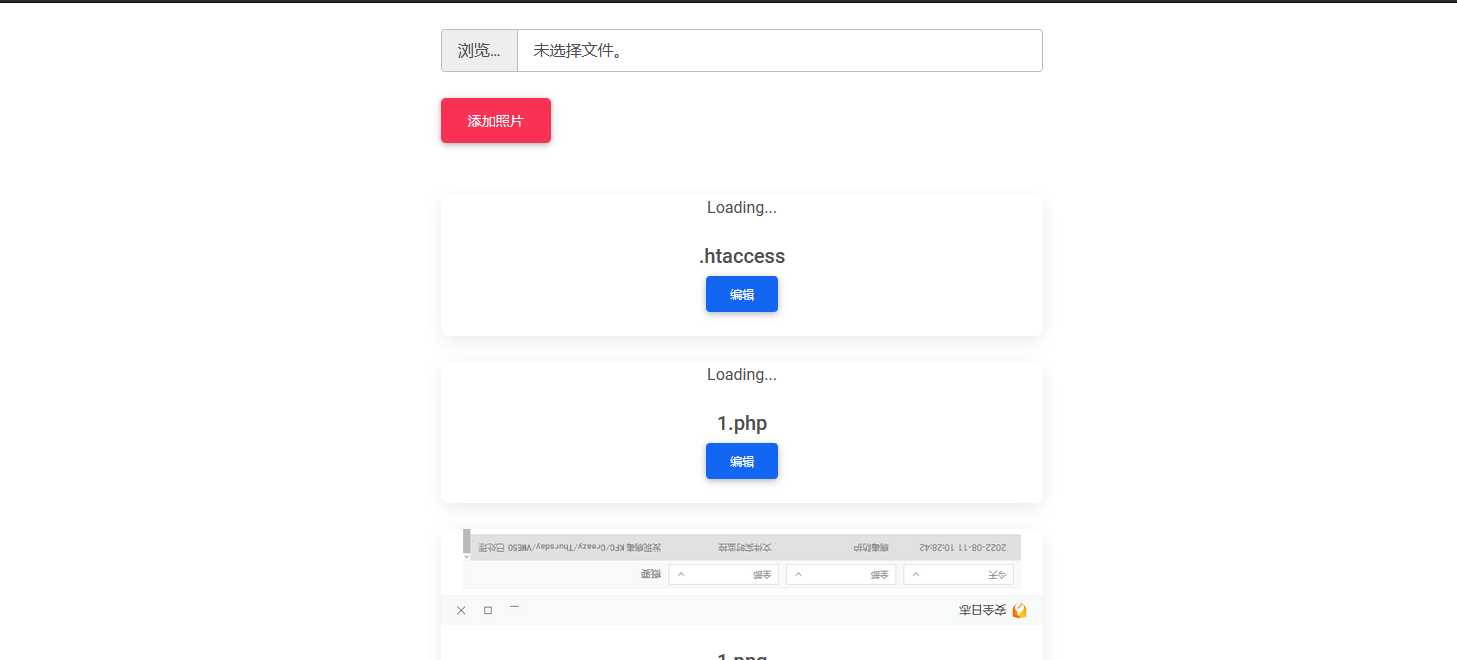
访问1.php只会出现404not found这是最令人异或的一点
因为题目给了docker,就本地部署一个环境,先进去看看文件都存到了哪里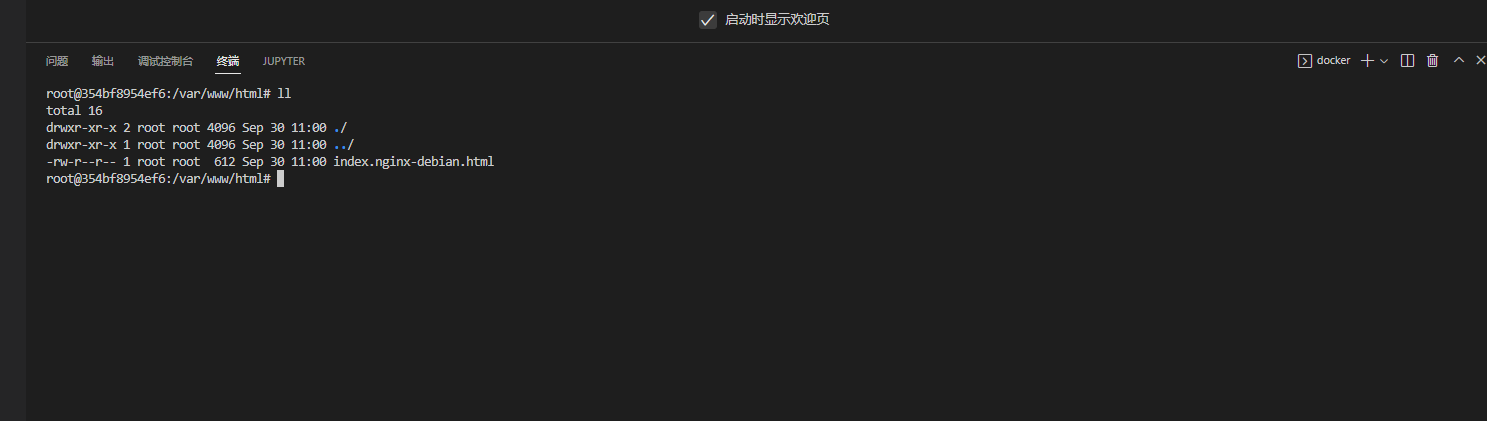
可以看见,文件并没有被上传到/var/www/html/这个目录下面
而文件被上传到了/var/www/html/mako/uploads这个目录下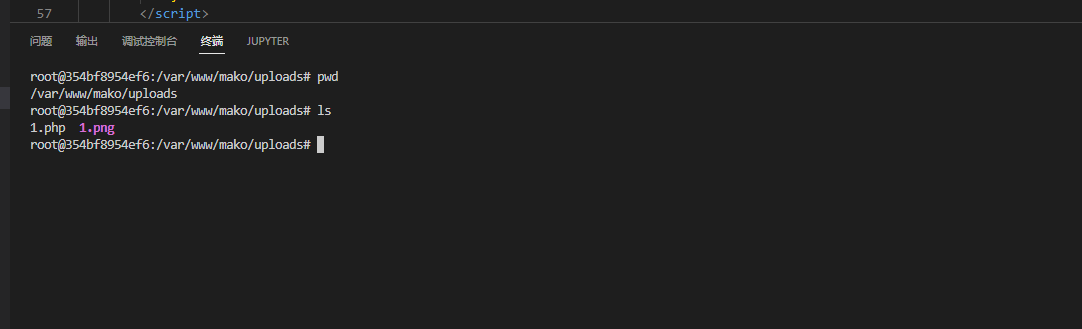
可以肯定的是,文件上传是整不了活了
通过搜索关键词,在mako/app/reources/views/home.tpl.php里找到到了首页的源码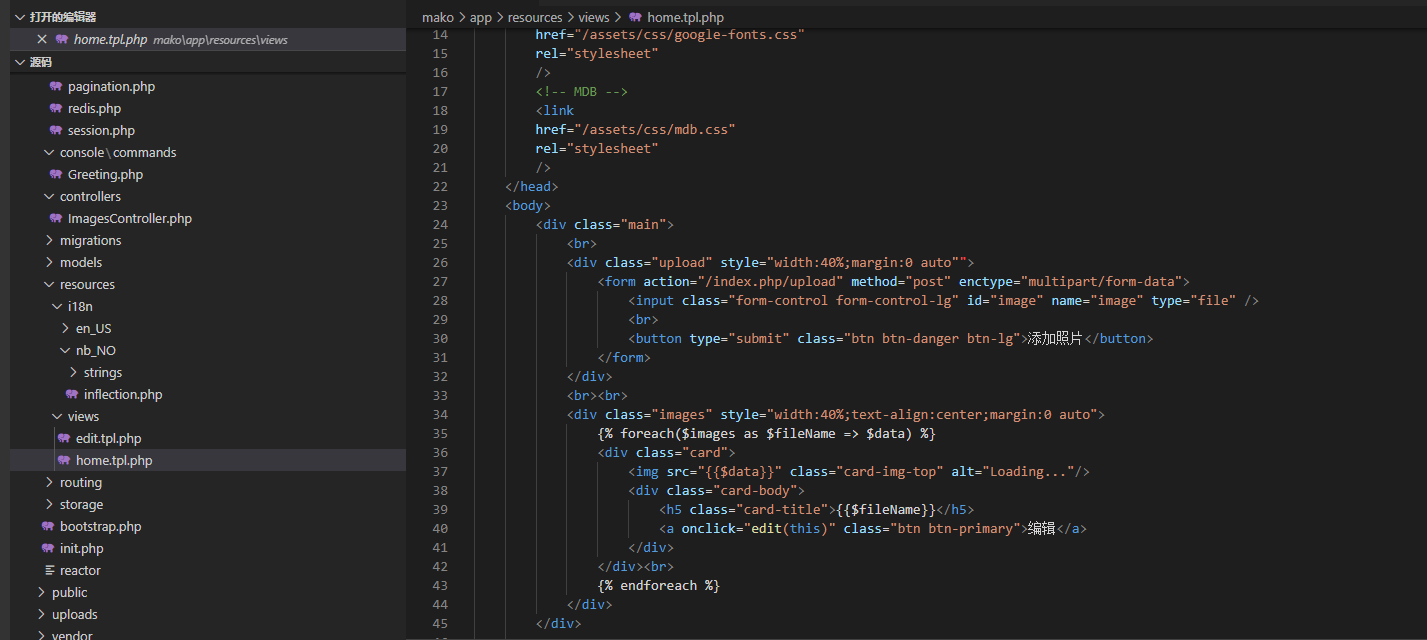
很明显,这是用模版渲染出来的主页, 图片都是以base64的编码形式传递的,没活整了。
这就很令人苦恼,我当时尝试了一下,使用软链接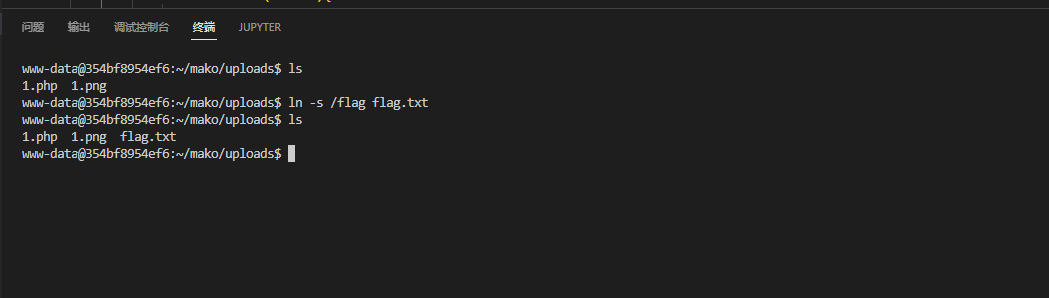
直接寄了,没权限,这时候才想起来容器一开始写了一个读取flag的程序
目标也明确了,肯定得想办法执行readFlag,于是我搜了危险函数,然后是一无所获,要么没这个函数,要么根本无法触发
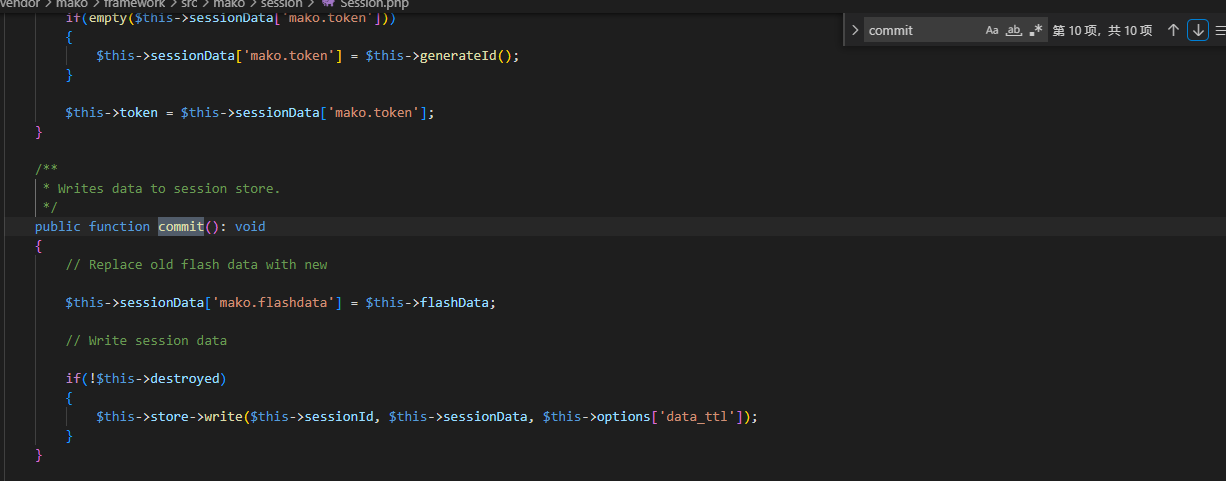
做到这里,我已经没有思路了,当时想到了反序列化,但是只知道搜unseralize,结果是毛都没搜到。
我经验太少了,当时没想到用phar
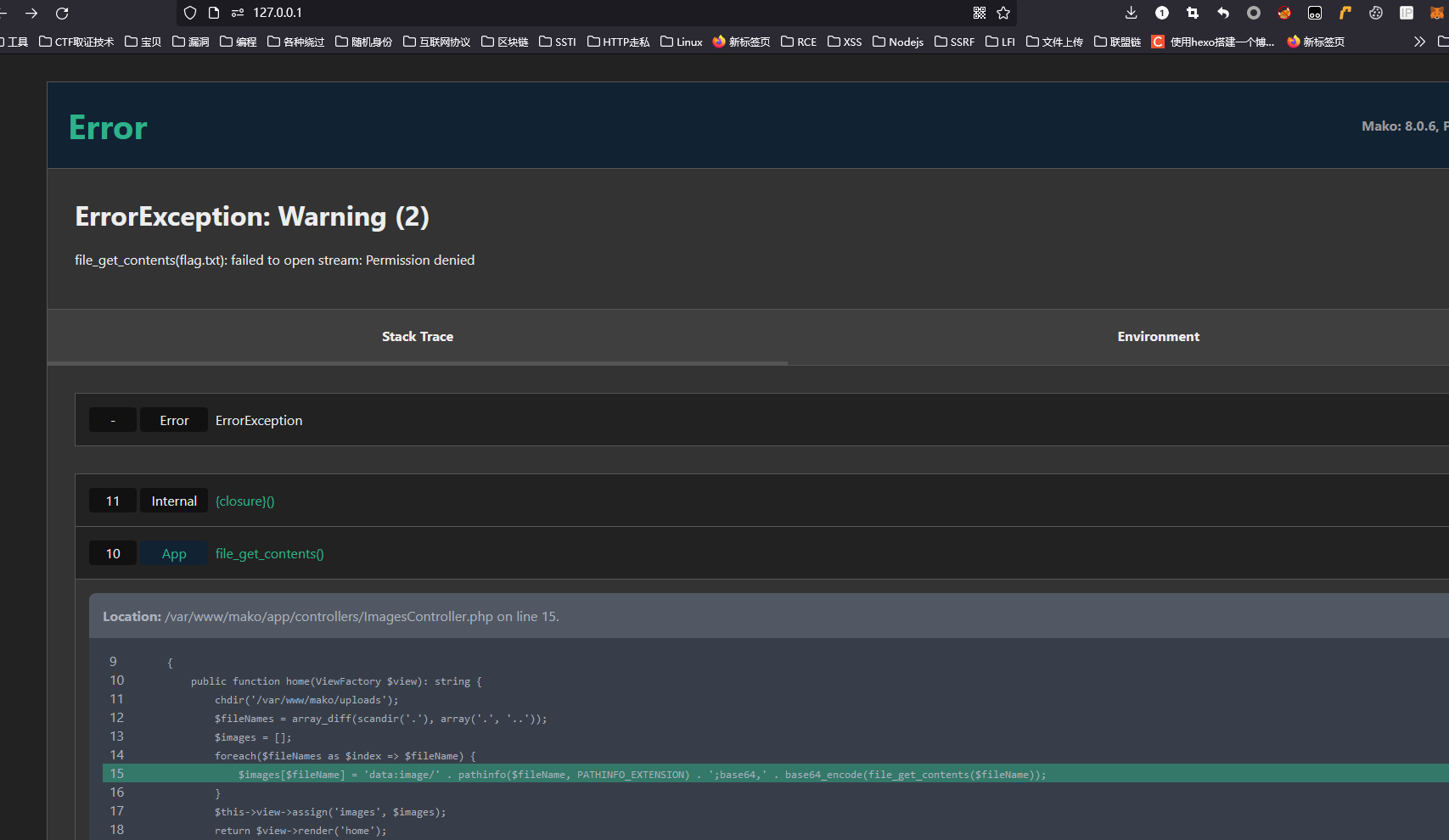
在mako/app/controllers/ImagesController.php文件中
1 | public function editGet(ViewFactory $view): string { |
可以看到,文件名是不做任何过滤的
而在mako/vendo/mako/framework/src/mako/pixl/image.php中
1 | public function __construct($image, ProcessorInterface $processor) |
使用了能触发phar反序列化的file_exists函数
关键函数找到了,现在找链子吧
搜索__destruct(),干扰项不多,可以直接开撸

好家伙,我直接好家伙,一条龙服务了属于是qwq
这里搬一手Arr3stY0u战队的poc吧
1 |
|
上传文件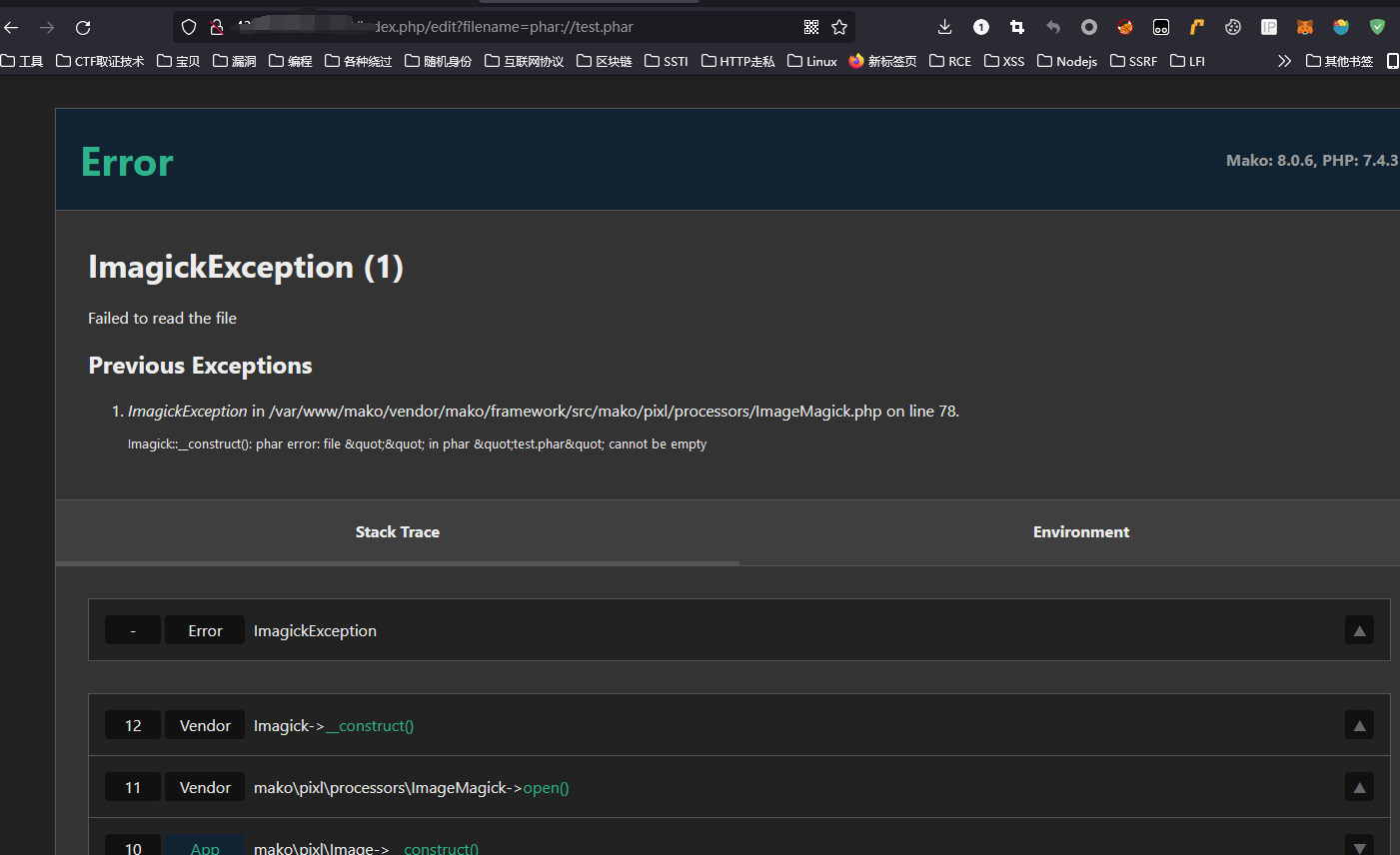
getshell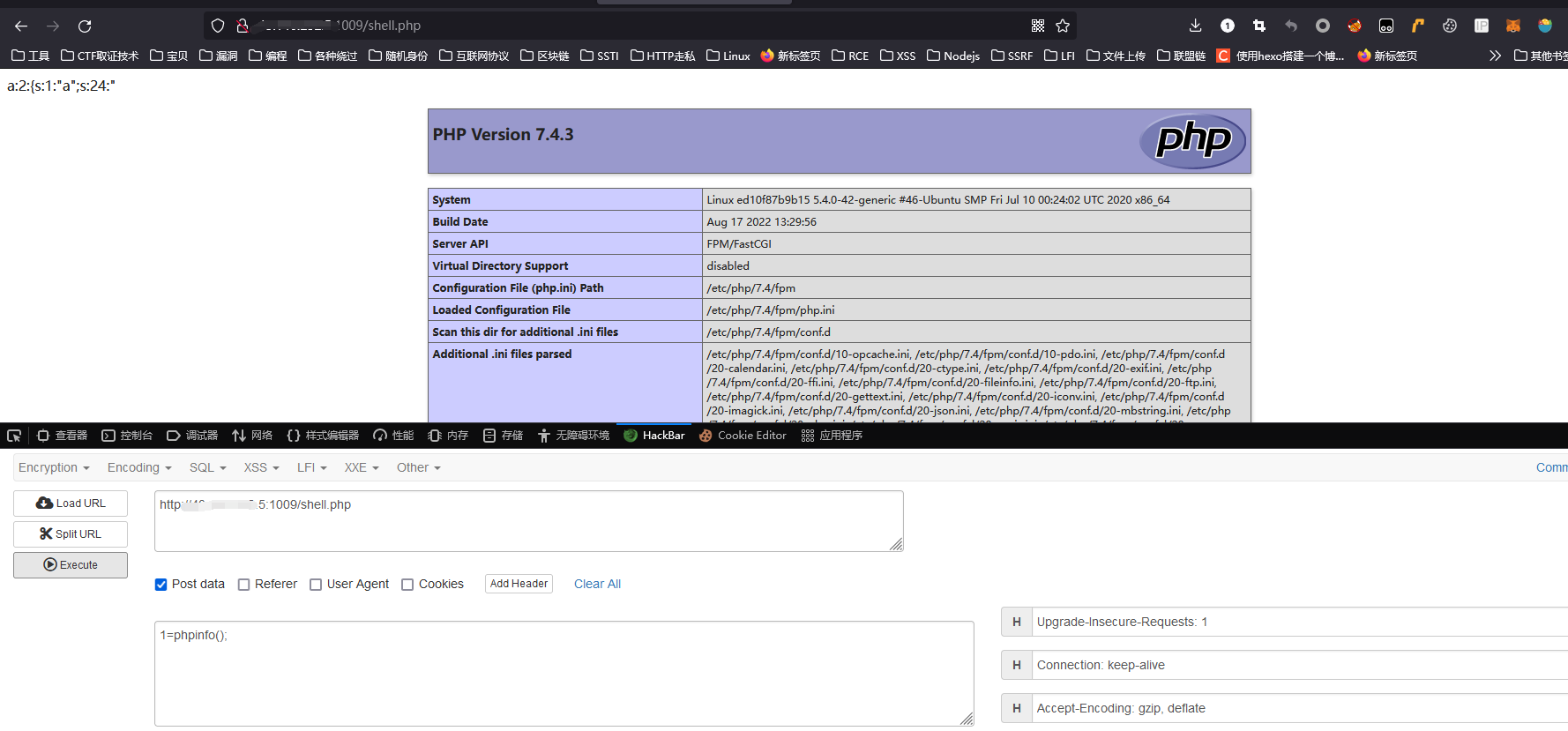
flag is here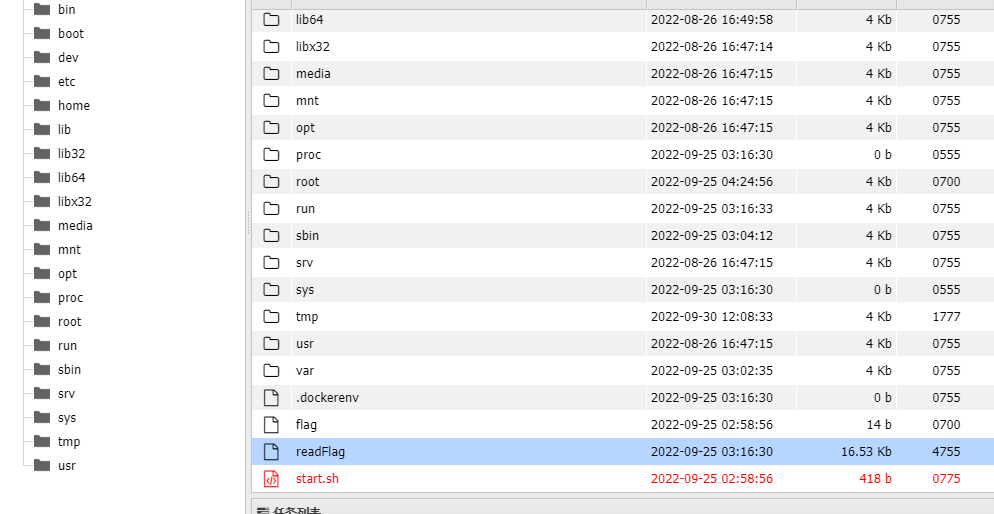
经验不足,做题不够,欠练